My burn-up chart for the current sprint has a "completed" line that nicely intersects the sprint guideline, so I can take a moment this Monday morning to eat lunch and read some news stories:
And closer to home—like, less than a kilometer away—the City of Chicago has made some recommendations to improve a stretch of Clark Street that could be a model for other streets in the city.
It got practically tropical this afternoon, at least compared with yesterday:
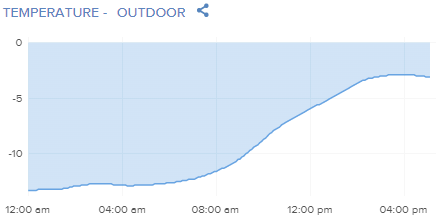
Cassie and I took advantage of the no-longer-deadly temperatures right at the top point of that curve to take a 40-minute, 4.3 km walk. Tomorrow should stay as warm, at least until the next cold front comes in and pushes temperatures down to -18°C for a few hours Thursday night.
I'm heading off to pub quiz in a few minutes, so I'll read these stories tomorrow morning:
OK, off to empty the dog, refill the dog, and scoot over to Sketchbook Skokie for a shellacking. (Our sports person can't make it tonight.)
I have no idea. But today I managed to get a lot of work done, so I'll have to read these later:
Finally, if you live in Chicago and look straight up and slightly north with binoculars tonight, you might see a little green comet that last passed Earth 50,000 years ago.
Accused fraudster Sam Bankman Fried did what every prosecutor hopes a defendant will do: start a blog. Researcher Molly White annotated his first post:
Sam Bankman-Fried has apparently decided to fill his time spent confined to his parents' Palo Alto home with blogging, perhaps in the hopes that he can just blog his way out of the massive criminal and civil penalties he's facing.
Although many of his statements here repeat things he's said elsewhere, I think it is useful to be able to analyze some of the story he's trying to spin all in one place, rather than cobbling his narrative together from multiple sources.
It's remarkable the extent to which SBF outright lies, or at the very least twists his version of events to distort reality in his favor. I don't intend to annotate further posts from him—which I suspect will be many—but instead hope that this will be sufficient to give some idea of just how thoroughly misleading his statements are.
Sample annotation:
If I was going to try to pick out a crypto firm that suffered large losses in an attempt to say "look, it was happening to everyone!", I might not pick the one whose founders have allegedly been in hiding for the last six months.34
And this:
It's clear that SBF's definition of "accurate" differs from most people's. SBF seems to think that if you tell someone that you have $1,000, and then later you say "...in monopoly money", it was still an accurate and defensible statement.
You know, I'm beginning to think 2023 will be the year people lose patience with lying fraudsters.
New Zealand's prime minister, Jacinda Arden, just resigned unexpectedly, which is a much more surprising story than any of these I queued up:
Finally, I'm glad to discover that ibuprofen may be more effective than acetaminophen for treating tension headaches, so I will now take one.
I'm on hold with my bank trying to sort out a transaction they seem to have deleted. I've also just sorted through a hundred or so stories in our project backlog, so while I'm mulling over the next 6 months of product development, I will read these:
And my bank's customer service finally got back to me with the sad news that the thing I wanted them to fix was, and we are so sorry, it turns out, your fault. Fie.
We get one or two every year. The National Weather Service predicts that by Friday morning, Chicago will have heavy snowfall and gale-force winds, just what everyone wants two days before Christmas. By Saturday afternoon we'll have clear skies—and -15°C temperatures with 400 mm of snow on the ground. Whee!
We get to share our misery with a sizeable portion of the country as the bomb cyclone develops over the next three days. At least, once its gone and we have a clear evening Saturday or Sunday, we can see all five of the naked-eye planets just after sunset.
Meanwhile, I'm about to start my team's Sprint 75 Review, the last one of 2022, which contains a few goodies we put off because we spent most of our time on client requests. We have a strange habit of doing what paying customers know they want before we add the things they don't know they want.
Meanwhile, elsewhere in the world:
Finally, director James Cameron ended all debate about whether Jack and Rose could both have survived in Titanic: "Cameron maintains that Jack simply had to die, telling The Sun that 'if I had to make the raft smaller, it would have been smaller.'" Because the story, you see, required it.
My drivers license expired in 2020, when all the Secretary of State's offices (what we in Illinois call the DMV) were closed, so I just renewed it online. I had hoped to upgrade to a Real ID, but it turned out the 2021 deadline for getting one got pushed back to 2023.
Since I moved in October, I actually have to go to the SOS office as they won't accept address changes online. But I still don't need a Real ID, it turns out:
Americans will have two more years to obtain a Real ID driver’s license or identification card, the Department of Homeland Security announced Monday.
U.S. air travelers will be required to present the Real ID credential to board a domestic flight beginning May 7, 2025. Before Monday’s announcement, implementation had been scheduled to take effect in May next year.
Postponing enforcement of the last phase of the Real ID Act will give motor vehicle departments across the country more time to process the new credentials, but will come 17 years after the changes initially were to be in place. States have reported that progress on the Real ID program was hindered by the coronavirus pandemic.
In any event I already have both a passport book and a passport card. But still, how has it taken 17 years to get this done?
Even though I'm president of a medium-sized non-profit organization who understands the importance of keeping in touch with constituents, I have run out of patience. For the last couple of weeks, I have mercilessly unsubscribed from every mailing list that sent me more than two emails a week. I might wind up missing a couple of them, but my dog, some of them just would not shut up.
The worst offender was my undergraduate university. In the last week, until I finally unsubscribed from them just now, they've sent me about 20 emails asking for money. "Last chance!" "Really last chance!" "Our matching fund expires in two hours!" "Our matching fund expires in 30 minutes!" "Our matching fund expired just now but send us a couple of bucks anyway!"
Actually, that's not true: the worst offender—even post-election—is my political party, because I've given to so many campaigns over the years. Listen, swing-state Senator: I gave you $100 in 2018, you won, stop bothering me. I'm not giving you more money until 2024. And I'm annoyed you've sent me about 825 emails on behalf of every other member of the Democratic Party in your state.
STFU. Just, STFU.
My organization decided not to send a Giving Tuesday email this year, and we've limited email blasts to two on behalf of partner organizations promoting actual performances and one for ourselves promoting Messiah (tickets still available!). Even then, our unsubscribe rate hit record levels this week. Maybe there's a correlation?
I know fist-hand how difficult non-profit organizations have it this year. But please, guys, stop with the emails. Just. Stop.
</rant>
Via Bruce Schneier, Ars Technica describes in painful detail how computer repair people snoop and steal people's data all the time:
If you’ve ever worried about the privacy of your sensitive data when seeking a computer or phone repair, a new study suggests you have good reason. It found that privacy violations occurred at least 50 percent of the time, not surprisingly with female customers bearing the brunt.
Researchers at University of Guelph in Ontario, Canada, recovered logs from laptops after receiving overnight repairs from 12 commercial shops. The logs showed that technicians from six of the locations had accessed personal data and that two of those shops also copied data onto a personal device. Devices belonging to females were more likely to be snooped on, and that snooping tended to seek more sensitive data, including both sexually revealing and non-sexual pictures, documents, and financial information.
The amount of snooping may actually have been higher than recorded in the study, which was conducted from October to December 2021. In all, the researchers took the laptops to 16 shops in the greater Ontario region. Logs on devices from two of those visits weren’t recoverable. Two of the repairs were performed on the spot and in the customer's presence, so the technician had no opportunity to surreptitiously view personal data.
In three cases, Windows Quick Access or Recently Accessed Files had been deleted in what the researchers suspect was an attempt by the snooping technician to cover their tracks. As noted earlier, two of the visits resulted in the logs the researchers relied on being unrecoverable. In one, the researcher explained they had installed antivirus software and performed a disk cleanup to “remove multiple viruses on the device.” The researchers received no explanation in the other case.
In all, the findings from the study were:
• Privacy policies and the practice of communicating protocols and controls to protect customers’ data do not exist across service providers of all sizes.
• Service providers largely (10/11) require “all access” to the device, even when it is unnecessary.
• Technicians often snoop on customers’ data (6/16) and sometimes copy those to external devices (2/16).
• Technicians who violate privacy often do so carefully to not generate evidence (1/6) or remove such evidence (3/6).
• A significant proportion of broken devices (26/79, 33 percent) are not repaired due to privacy concerns. For the devices that get repaired, device owners are concerned about threats to their privacy but do not use the proper controls to protect their data.
The results likely confirm what many more experienced computer users already know: that their data is vulnerable to snooping or copying any time they surrender their device to an untrusted or unknown individual, particularly when the individual has their login password. But for a much larger percentage of people wanting to recover crucial data on a broken device, the findings are likely a wake-up call with few, if any, good solutions.
Another way to look at it: do you trust your locksmith?