I stumbled upon this commercial from the 1980s that ran in the UK:
Definitely John Cleese. (And what the hell has 4.1 megabytes?)
I kind of got into the flow today, so things to read later just piled up:
And wait—you can make risotto in an Instant Pot? I might have to try that.
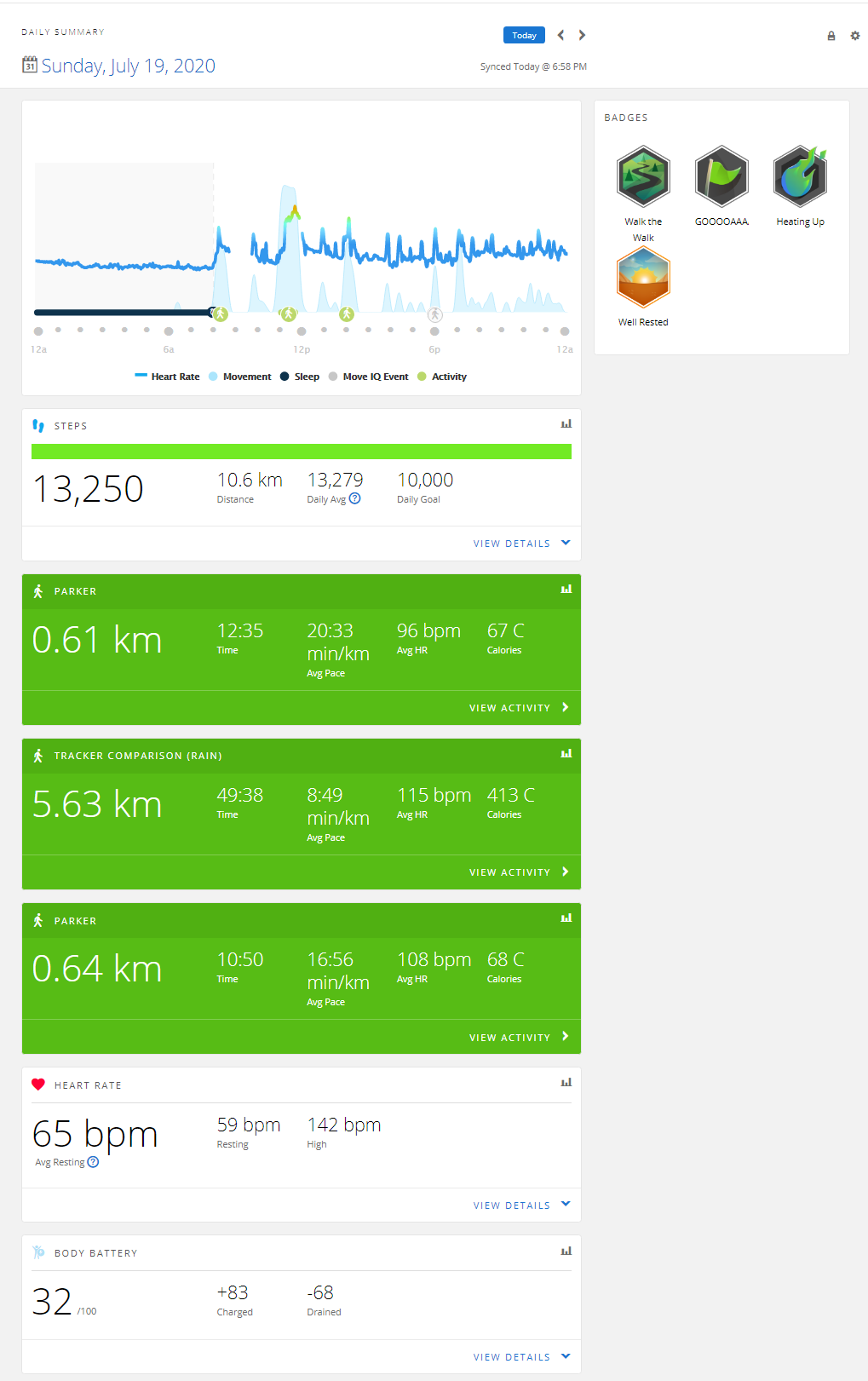
I wore both my old Fitbit Ionic and new Garmin Venu for about 42 hours straight. Yesterday they overlapped for the entire day. And they came in with similar, but not quite the same, numbers.
I thought that my Fitbit would record fewer steps overall, because it recorded about 450 (about 7%) fewer on my walk yesterday. For the whole day, though, the Fitbit counted 14,190 to the Garmin's 13,250—7% more. But I wore the Fitbit on my right (dominant) wrist, so it may have just had more activity in general.
In other basic measures:
- The Fitbit recorded 13.3 km to the Garmin's 10.6 km;
- The Fitbit estimated my resting heart rate as 64 to the Garmin's 65;
- Fitbit counted 82 "active" minutes to the Garmin's 359 "moderate" and 369 "vigorous";
- Fitbit estimated my calorie burn at 3,100 to Garmin's 2,862.
I have no way to know which tracker was more accurate, but I might bet a dollar on the Garmin. I think the Garmin used actual distance to the Fitbit's estimate based on my usual stride length, which doesn't account for all the difference.
The Garmin's app presentation is so far beyond Fitbit's I wonder whether Fitbit even has software developers. Here's Fitbit:

Here's Garmin's:
And that's not even all of the Garmin data.
I walked halfway home after work today, and once again, the Garmin tracked my workout better than the Fitbit has done in months.
I'm glad I switched.
Yeah, the Garmin wins, hands down.
After realizing that my first head-to-head test pitted an Ionic whose GPS was failing against a treadmill exercise, I went out for a quick loop around the block with both trackers correctly set to "Walk."
The Garmin found a GPS signal in about 20 seconds. The Fitbit never did.
After the walk, the Garmin produced this delightful map, complete with weather report and options for different maps:
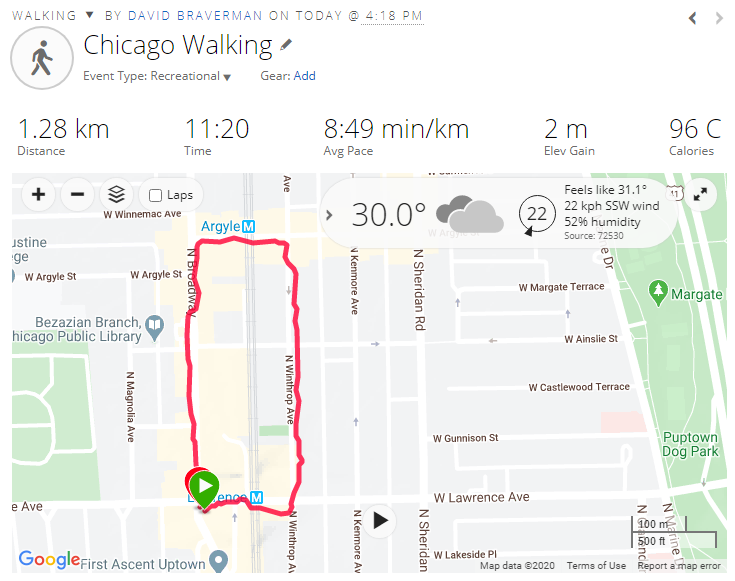
Right on the activity view, I've got a gear icon with these options:
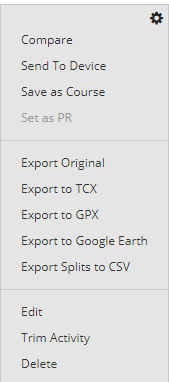
Fitbit only exports TCX files. Or you can export your entire account archive, become a programmer like me, parse your archive, and extract the relevant item.
But the map and export options just scratch the surface. Look what the Fitbit Web app gives me for this walk (since it didn't have GPS):

And here's the Garmin:
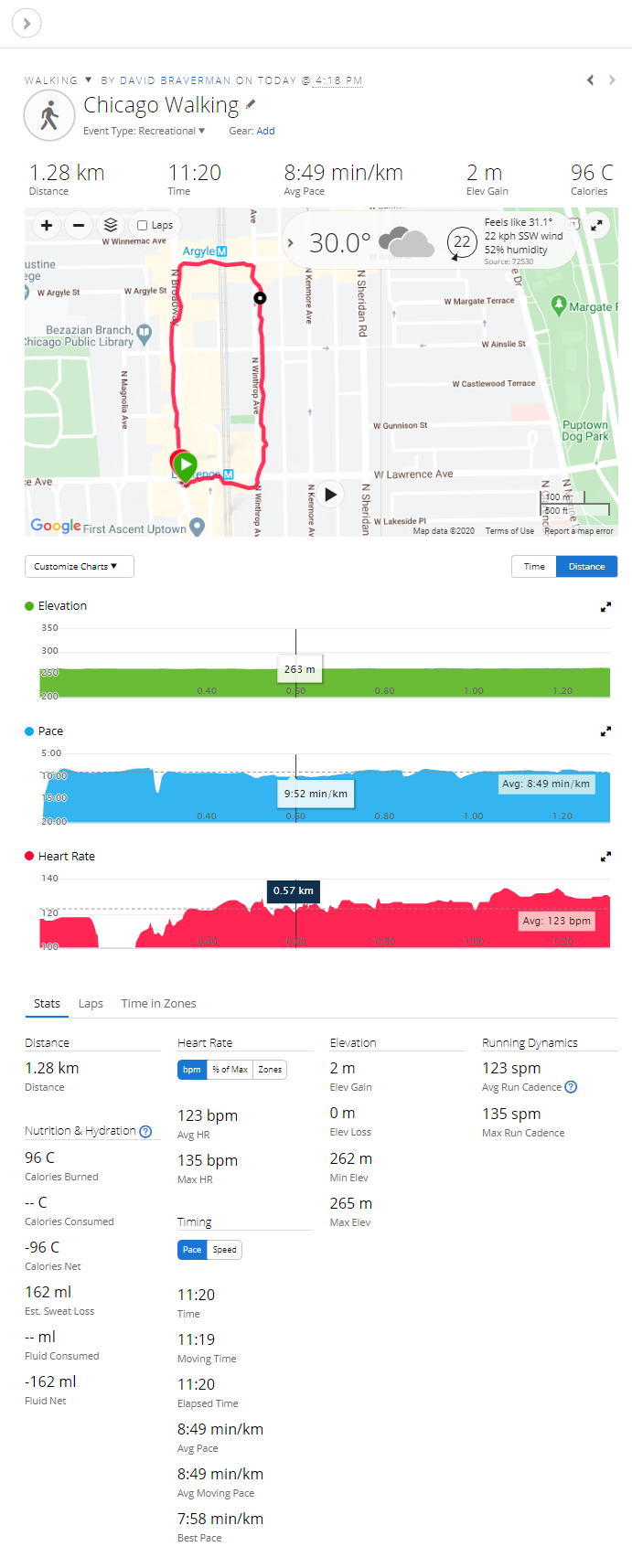
I mean, that's not even fair. Garmin even gave me the weather report, fer gassake. (It did not give me the step count for the activity, though.
Yeah. Fitbit, you were great, but I've grown; you haven't. You fell so far behind Garmin that I don't know how you're going to catch up.
Tonight, I'll see how differently they track sleep. And I hope that I can re-import today's Fitbit steps, else I'll lose the 7,000 I had before I set up the Garmin. Also, Garmin only imports step counts, intensity times, and body mass from Fitbit, not sleep data, so I'll have to find a different solution for that.
My day kept getting longer as it went on in a way that people living through the pandemic will understand. So I didn't have time to read any of these yesterday:
Finally, Jon Oliver has put out a line of Last Week Tonight stamps to help support the US Postal Service. So naturally I bought some.
Welcome to day 31 of the Illinois shelter-in-place regime, which also turns out to be day 36 of my own working-from-home regime (or day 43 if you ignore that I had to go into the office on March 16th). So what's new?
Oy:
Finally, via Bruce Schneier, the Dutch intelligence service had an unintentional back door into several other countries' communications. (Scheier says, "It seems to be clever cryptanalysis rather than a backdoor.")
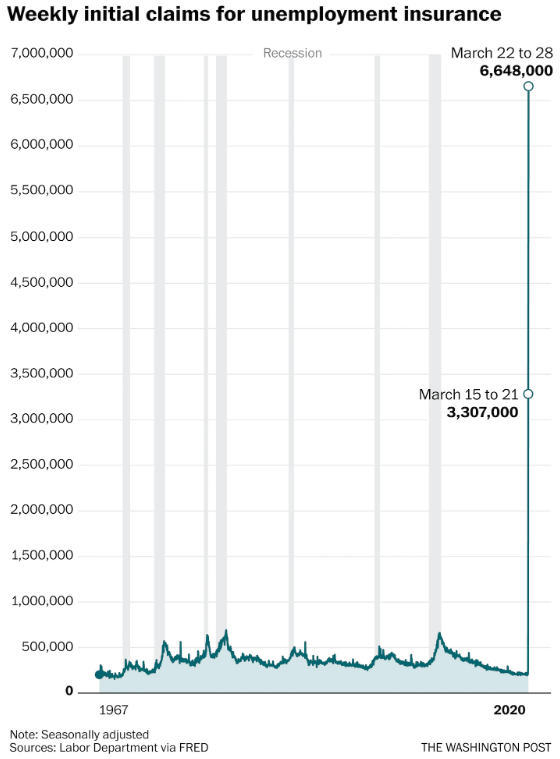
More than 6.6 million Americans filed for unemployment insurance last week (including 178,000 in Illinois), following the 3.3 million who filed the week before. This graphic from The Washington Post puts these numbers in perspective:
Hotel occupancy has crashed as well, down 67% year-over-year, with industry analysts predicting the worst year on record.
In other pandemic news:
Finally, unrelated to the coronavirus but definitely related to our natural environment, the Lake Michigan/Huron system recorded its third straight month of record levels in March. The lake is a full meter above the long-term average and 30 cm above last year's alarming levels.
I had a lot going on at work today, so all I have left is a lame-ass "read these later" post:
I'd say "back to the mines," but I believe I have a date with Kristen Bell presently.
First event: Last night around 7pm, my main data drive seized up after storing my stuff for a bit less than 4 years. Let me tell you how much fun Micro Center is at 9pm two days before Christmas. After 12 hours it looks like it's about 75% restored from backup, and I didn't suffer any data loss.
Second event: Just look at this lovely, peaceful scene:

That's the cemetery in my neighborhood a few minutes ago. And that's what we call "dense fog," with about 200 m visibility and what they call "indeterminate" ceilings at 100 m.
Which is exactly what you want in Chicago on Christmas Eve, the second-biggest travel day of the year:
Amid dense fog reducing visibility in Chicago, the Federal Aviation Administration early Tuesday grounded incoming flights at Chicago’s O’Hare International and Midway airports until at least 8 a.m.
For a short time Tuesday morning all flights were grounded, according to the FAA, but as of 7:30 a.m. the agency’s website noted the “ground stoppage,” or halting of flights, was indicated only for airplanes arriving at the city’s two airports. Flights were departing regularly at Midway, according to travelers at the airport.
Still, the ground stoppage for incoming flights means not all departing flights will leave on time and travelers could miss connecting flights, leading to a chain-reaction of air travel delays during a traditionally peak period for travel.
Have a safe and fun travel day, and if you're going to or through Chicago, enjoy your airport time.
My 5-year-old Microsoft Surface, which I use at work to keep personal and client concerns physically separated, has died. I thought it was the power supply, but it seems there is something even more wrong with it. Otherwise I would have posted earlier.
This means I have to make an expensive field trip tonight. Regular posting should resume tomorrow.